Show Updates
Final Program Announced for May 12 Cybersecurity, Content Protection Summit
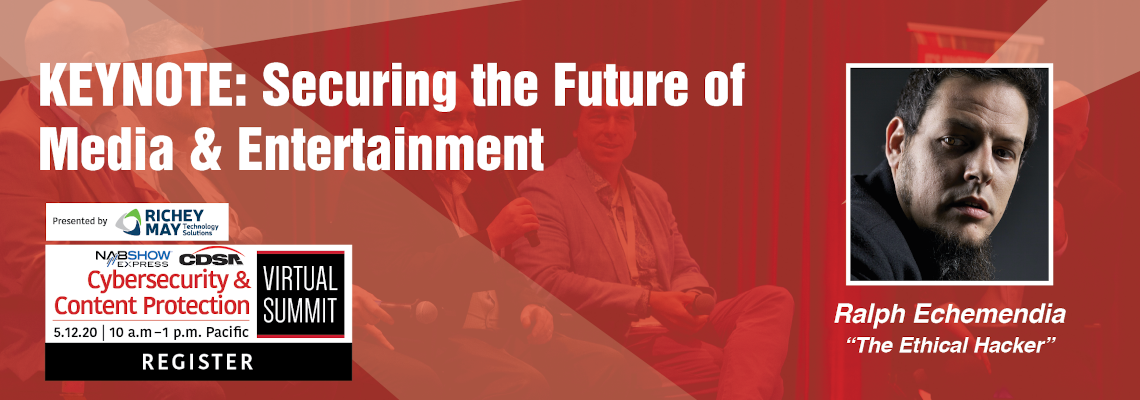
A keynote presentation by the cybersecurity specialist known as “The Ethical Hacker,” a bevy of vendor presentations covering everything from the cloud to digital screeners, studio presentations around how they view securing home work stations, and industry updates from the Content Delivery & Security Association (CDSA) and the Trusted Partner Network (TPN).
All that and more is on tap May 12 during the annual Cybersecurity & Content Protection Summit (CCPS), being held digitally as part of the NAB Show Express experience, as the M&E security industry at large gathers to share what they’ve learned during the ongoing remote work reality. Continue reading
May 12 Cyber, Content Protection Summit: Protecting the New M&E Normal
From planning against insider threats, to keeping screener content safe. Securing the cloud, to identifying cybersecurity weakness in advance. And all in the context of protecting the industry’s assets — and securing home work environments — during today’s new remote production reality.
Those are the insights members of the Media and Entertainment Services Alliance (MESA) are bringing to the May 12 Cybersecurity & Content Protection Summit, being held digitally as part of the NAB Show Express experience. Continue reading
Richey May Technology Examines Work-From-Home Security Implications May 12
Business continuity plans have been activated, production editing at home is the new normal, and absolutely everyone’s video conferencing. As for whether all of that is secure, though, remains to be seen.
That’s the message Michael Wylie, director of cybersecurity services for Richey May Technology Solutions, will bring to the forefront May 12 during his presentation at the annual Cybersecurity & Content Protection Summit, being held digitally as part of the NAB Show Express experience. Continue reading
CDSA’s Cybersecurity & Content Protection Summit and TPN Returns to NAB
Just a couple months ago, work-from-home was a nice-to-have option — one treated with skepticism by executives — for those in the media and entertainment space. The COVID-19 pandemic has quickly made it a critical necessity in order to keep business running. And with this new reality comes a new front in the cybersecurity and content protection battle the industry has waged for decades.
From choosing the most-secure-possible workflow, cloud and storage solutions available to facilitate a fully remote workforce; to discovering gaps in now-crucial business continuity plans; to evaluating threats to your intellectual property where your workforce is dispersed outside the office, the concerns — and threats — are like nothing media and entertainment has encountered before. Continue reading